TL;DR
Security researchers have identified a zero-click exploit chain affecting the Pixel 10, leveraging a Dolby vulnerability and a driver flaw in the VPU component. The exploit can achieve root access on unpatched devices, highlighting ongoing security risks.
Researchers have uncovered a zero-click exploit chain for the Google Pixel 10, capable of gaining root access without user interaction on unpatched devices, marking a significant security concern.
The exploit chain builds upon a previously patched Dolby vulnerability (CVE-2025-54957), which was exploited on Pixel 9 devices. Updating this exploit for Pixel 10 required modifications to account for hardware differences, such as the use of RET PAC instead of -fstack-protector. Additionally, researchers identified a new vulnerability in the Pixel 10’s VPU driver, which is used for video decoding acceleration. This driver exposes hardware registers via an insecure mmap implementation, allowing an attacker to map arbitrary physical memory, including kernel regions, into user space. By exploiting this flaw, an attacker can overwrite kernel functions or gain arbitrary read-write access to kernel memory, facilitating privilege escalation. The vulnerability was reported on November 24, 2025, rated high severity by Android VRP, and patched within 71 days in the February security bulletin. The exploit requires the device to be unpatched (SPL December 2025 or earlier).
Why It Matters
This discovery underscores ongoing security challenges in Android devices, especially in hardware driver code, which can be exploited for privilege escalation. The rapid patching process demonstrates improvements in Android’s vulnerability response, but the existence of such flaws highlights the importance of more secure driver development practices to protect end-users.
Android security patch update for Pixel 10
As an affiliate, we earn on qualifying purchases.
As an affiliate, we earn on qualifying purchases.
Background
In January 2026, researchers demonstrated a zero-click exploit chain on Pixel 9 using a Dolby vulnerability, which was patched that month. Building on that, they adapted the exploit for Pixel 10, which introduced new hardware and software changes, including the use of RET PAC. The recent findings reveal that the Pixel 10’s VPU driver contains a critical flaw, allowing arbitrary memory mapping, which was not present or exploitable in earlier models. The discovery aligns with ongoing efforts by security researchers to identify and report Android vulnerabilities, pushing for faster patches and more resilient codebases.
“The VPU driver vulnerability allows mapping unlimited physical memory into user space, enabling arbitrary kernel memory access with just a few lines of code.”
— researcher
“The vulnerability was patched swiftly, reflecting our improved triage and response processes for high-severity issues.”
— Android VRP spokesperson
Pixel 10 VPU driver security fix
As an affiliate, we earn on qualifying purchases.
As an affiliate, we earn on qualifying purchases.
What Remains Unclear
It remains unclear whether other components in Pixel 10 or similar devices are vulnerable to comparable exploits. The full extent of the VPU driver flaw and whether it can be exploited remotely is still under investigation. Additionally, the current exploit chain only works on unpatched devices, and the effectiveness of potential future patches is unknown.
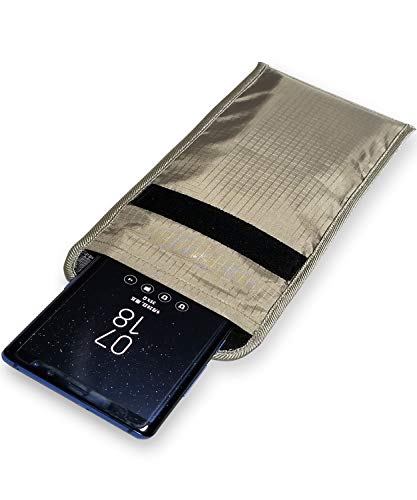
LVFEIER Security Pouch – Cell Phone Anti-Tracking Anti-Spying GPS RFID Signal Blocking Bag Shielding Pouch Wallet Case for Cell Phone Privacy Protection
POWERFUL CELL PHONE RADIATION PROTECTION: Reduces your exposure to cellular phone radiation by up to 99%, to shield…
As an affiliate, we earn on qualifying purchases.
As an affiliate, we earn on qualifying purchases.
What’s Next
Security researchers and Android developers will likely continue auditing Pixel 10 and other devices for similar vulnerabilities. Users are advised to update their devices to the latest security patches. Further research may reveal additional hardware or software flaws, and Android is expected to release updates to mitigate these risks.

Wireless and Mobile Device Security: .
As an affiliate, we earn on qualifying purchases.
As an affiliate, we earn on qualifying purchases.
Key Questions
Can this exploit affect all Pixel 10 devices?
No, the exploit only works on devices that have not yet received the security patch issued in February 2026.
Is this vulnerability exploitable remotely?
Based on current information, the exploit requires local access and unpatched firmware; remote exploitation has not been demonstrated.
What can users do to protect themselves?
Users should ensure their devices are updated with the latest security patches provided by Google.
Will future patches fix this vulnerability?
It is expected that Google will address this driver flaw in upcoming updates, but the timeline depends on ongoing assessments and testing.









